Instances of identity theft are on the rise around the globe due to such a high volume of the population using different forms of identification, using digital systems, and attackers becoming more intelligent in their attacks. And an area of identity theft is aggravated identity theft - an area which is often the scariest type of identity theft for many people.
Before we get into what aggravated identity theft is, we would like to point out that we have written a blog post here that can help identify the common red flags of whether someone is using your identity.
Identity theft is a crime where someone steals your personal information, like your name, address, or information on an identity document. Criminals then use that information to pretend to be you and do things like open new accounts in your name which can open doors to money laundering, terrorism funding, and fraudulent activities. Identity thieves may also use the victim's identity to commit other crimes, such as using their credit cards to make luxury purchases. With more and more people using digital devices such as phones and computers for daily tasks, it is becoming easier for identity thieves to steal personal information from unsuspecting victims.
Identity theft is a traumatic experience that many victims say takes away their sense of security and privacy. They often find themselves in an awkward state of hypersensitivity to their environment. Identity thieves can steal your financial assets and information, making you vulnerable to all types of fraud and scams.
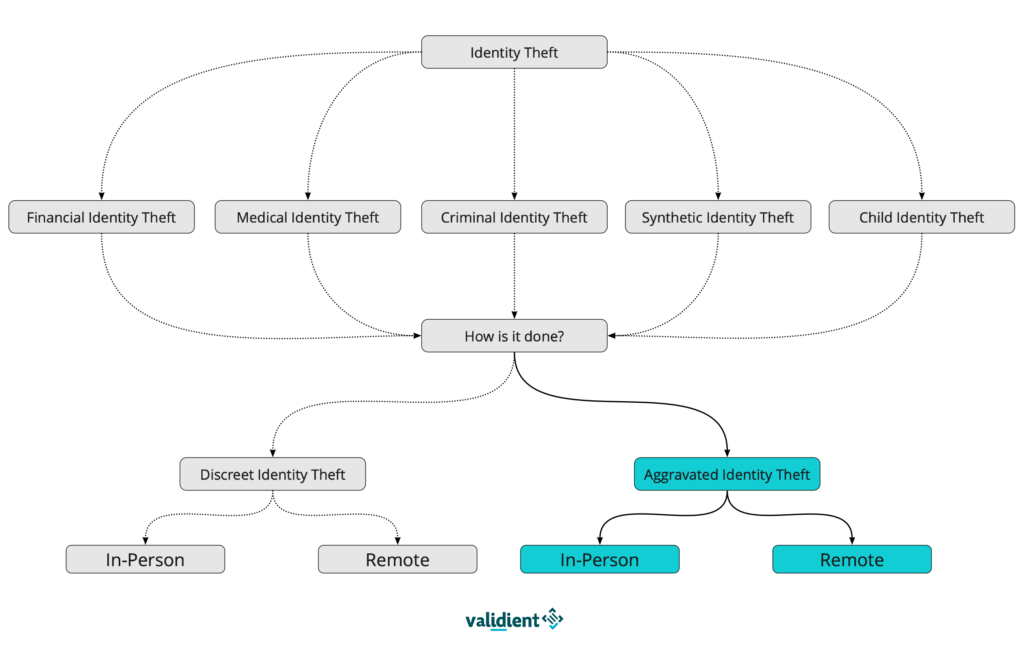
There are five key elements for identity theft attacks. These are:
- Financial Identity Theft
- Medical Identity Theft
- Criminal Identity Theft
- Synthetic Identity Theft
- Child Identity Theft
Identity theft can then be broken down further into two categories. These are:
- Discreet Identity Theft - when the victim is none the wiser and unaware of the theft
- Aggravated Identity Theft - when force or violence is used against the victim. This is what we are focusing on in this article
Now that we have touched on identity theft as a general concept, we will explore aggravated identity theft. Aggravated identity theft is searched over 800 times a month on Google - it is something that people are either worried about or are experiencing a lot. With around 1 in 15 people becoming victims of identity fraud, it's important to understand such topics.
Put simply, aggravated identity theft is a type of identity theft that involves the use of force or violence. This type of identity theft can be committed by an individual who has access to an individual's personal information and uses it or their own gain. Aggravated identity theft is typically committed in person through stolen possessions, but can also be committed remotely by hacking into systems. We will cover more on this in the next section.
There is a lot of information out there that looks at the different types of identity theft, but we want to focus here more on two types that are often forgotten about; the difference between in-person and remote aggravated identity theft. Remote is the more popular route for criminals to steal identity, but remote cases do still happen.
There are multiple cases of aggravated remote identity theft. But below we have listed different examples of it happening in the real world lately.
June 2022 - New York Man Sentenced to 24 Months for Aggravated Identity Theft
June 2022 - Health Care Fraud, Aggravated Identity Theft, and Illegally Prescribing Substances
May 2022 - Man Convicted of Misusing a Social Security Number and Aggravated Identity Theft
October 2021 - SIM Swappers Phished a Phone Company to Steal $16k in Crypto
In-person aggravated identity theft can range from someone finding your ID on the street and threatening you with fraudulent activity for a ransom, all the way to burglary such as pick-pocketing and break-ins. Some examples of in-person aggravated identity theft are below:
- Laptop and Computer Theft
- Private Documents such as Birth Certificates, Passports, Tax Returns, and Banking Documents
Fraudulent activity is governed by the UK Government in The Fraud Act 2006. The act provides for a range of offences relating to fraud, dishonesty, and false accounting. The Fraud Act 2006 was enacted to consolidate certain enactments relating to offences that involve fraud. The Act categorises fraudulent activities in three key ways:
- False Representation - if representation is false, it means that the person who is committing fraudulent activity knows that it is fraudulent or that it might be untrue
- Failing to Disclose Information - when a person is being dishonest and doesn't disclose information when under a legal duty to disclose
- Abuse of Position - when a person uses their position of trust (for example a police officer)to commit fraud by financially gaining from said position
The consequences of aggravated identity theft are severe and can include jail time and fines. The punishment depends on the severity of the crime as well as whether or not there was intent to commit fraud. Usually, for a planned identity theft crime, the consequences will be a prison sentence of anywhere between 2 and 7 years. However, prison time can increase depending on the seriousness of the crime, and who the victim was.
Generally, identity theft is one of the most serious crimes in the UK. In 2019, it was reported that at least 6% of respondents in the UK had experienced attempted identity theft in the last three years. Despite that number not sounding staggering, the question must be raised around how much stolen identity goes without seeing. As mentioned at the beginning of this article and in the visual, the two key types of identity fraud are aggravated and discreet. This shows how effective discreet identity fraud can be, and how 'on-guard' everyone should be.
Please see our other article here on how to know if you have been a victim of identity theft and what to do if you think you have been affected.
There are many ways that technology solutions can help combat identity theft. Below are a few ways that client onboarding systems such as Validient can help:
- Help spot false documentation using biometric analysis
- Produces risk profiles on companies and individuals to spot any abnormalities
- Reduces the risk of human error
If we can help your firm, please feel free to get in touch through the website or by emailing info@validient.com.